.jpg)
10 May 2022 POSTED BY DIYA Robotics
Cybersecurity: Sovereign Of Future
The term cybersecurity has become almost synonymous with other terms, such as IT security or information security. Of course, hackers possessing malicious intent to steal proprietary information pose the most significant threat to these assets.
In a world where every device is connected, convenience is one of the benefits: you can manage your social calendar, make appointments, shop, and conduct work from your device. In fact, many of us do these things even without thinking about the fact that we are addicted to those devices. Generally, technology was found to reduce the burden on humans but the evolution of technology has made humans slaves to those machines.
In an era when there are such strong attacks on large organizations, how are you going to prepare your child for this? DIYA provides creative solutions to all your problems and agony. Join your child at DIYA to help them acquire knowledge on cybersecurity and tackle all situations without any effort on your part.
In general, the world faces five types of security threats. Let's have a look at them!
● Critical infrastructure security
● Application security
● Network security
● Cloud security
● Internet of Things (IoT) security
1. Critical infrastructure security
In the area of critical infrastructure security, concerns revolve around protecting systems, networks, and assets whose efficient and effective operation is necessary for the security of a nation, its economy, and the public's health and safety. It is feasible to prevent and mitigate the fallout of a breach and mitigate the risks associated with internet-connected industrial control systems, including the impact an attack may have on a city or country, by applying security technologies and best practices.
2. Application Security
Through application security, software code and data are protected from cyberattacks. Application security can be applied throughout all stages of development, including design, development, and deployment. Security features of an application include authentication, authorization, encryption, logging, and application security testing. Security vulnerabilities can also be minimized through coding. A range of tools is used to secure applications, such as Web Application Firewall (WAF), Runtime Application Self-Protection (RASP), Software Composition Analysis (SCA), SAST, DAST, and so on.
3. Network security
Network Security safeguards your network and data from breaches, intrusions, and other threats. As a general term, this refers to hardware and software solutions, as well as rules and configurations regarding network use, accessibility, and overall threat protection. Regardless of whether it's a home network or a work network, network security is essential. Wireless routers are common in homes with high-speed internet connections; however, if not secured properly, they could be exploited. Data loss, theft, and sabotage are reduced when the network security system is solid.
4. Cloud Security
An array of security measures is designed to safeguard data, infrastructure, and applications in the cloud, also known as cloud computing security. Authentication of devices and users, control of data access, and privacy protection are among these measures. Cloud computing can be categorized into four main groups: Public cloud services include software-as-a-service (SaaS), infrastructure-as-a-service (IaaS), and platform-as-a-service (PaaS). By using cloud-based web security, traffic is directed to the cloud instead of being routed to servers. Using cloud-based technology, the cloud analyzes traffic and grants access only to authorized users. Cloud-based traffic that does not meet certain requirements is blocked from reaching the server.
5. Internet of Things (IoT) security
For IoT objects to work successfully, they need to be secure in terms of hardware, software, and connectivity. Integrated IoT devices, including refrigerators and manufacturing robots, are susceptible to being hacked without security. In the event of hacker control, they are able to usurp the object's functionality and steal its data. Nearly every technological device, from watches to thermostats to video game consoles, has the ability to connect to the internet or interact with another device in some way. These devices are protected from being compromised with a variety of techniques, strategies, and tools.
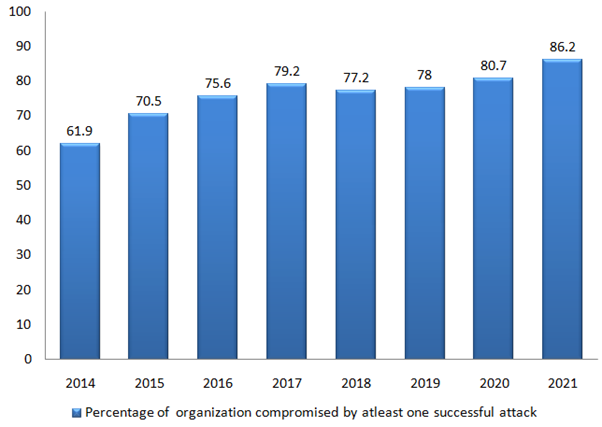
Due to the increase in business applications moving to private and public clouds in today's hyperconnected world, network security has become more challenging. Furthermore, modern applications are now often virtualized and distributed across many locations, some of which are outside the control of IT, security teams. Protection of network traffic and infrastructure is essential now that the number of attacks against companies has increased. Not only there is an increase in cybercrime, but also there is development in the study of cyber security.
Consequently, the modern world may change with its modern era, in addition to that, we need to change ourselves to deal with it. Educate your children in cyber forensics by joining them at DIYA . Sign up now & avail exciting offers.